Security
Physical. Digital. Secured.Proper security, logical and physical, is a business essential. Organizations of all sizes collect, store and use data. The increasing frequency of data breaches and cyberattacks highlight the growing responsibility to secure your data, networks and devices.
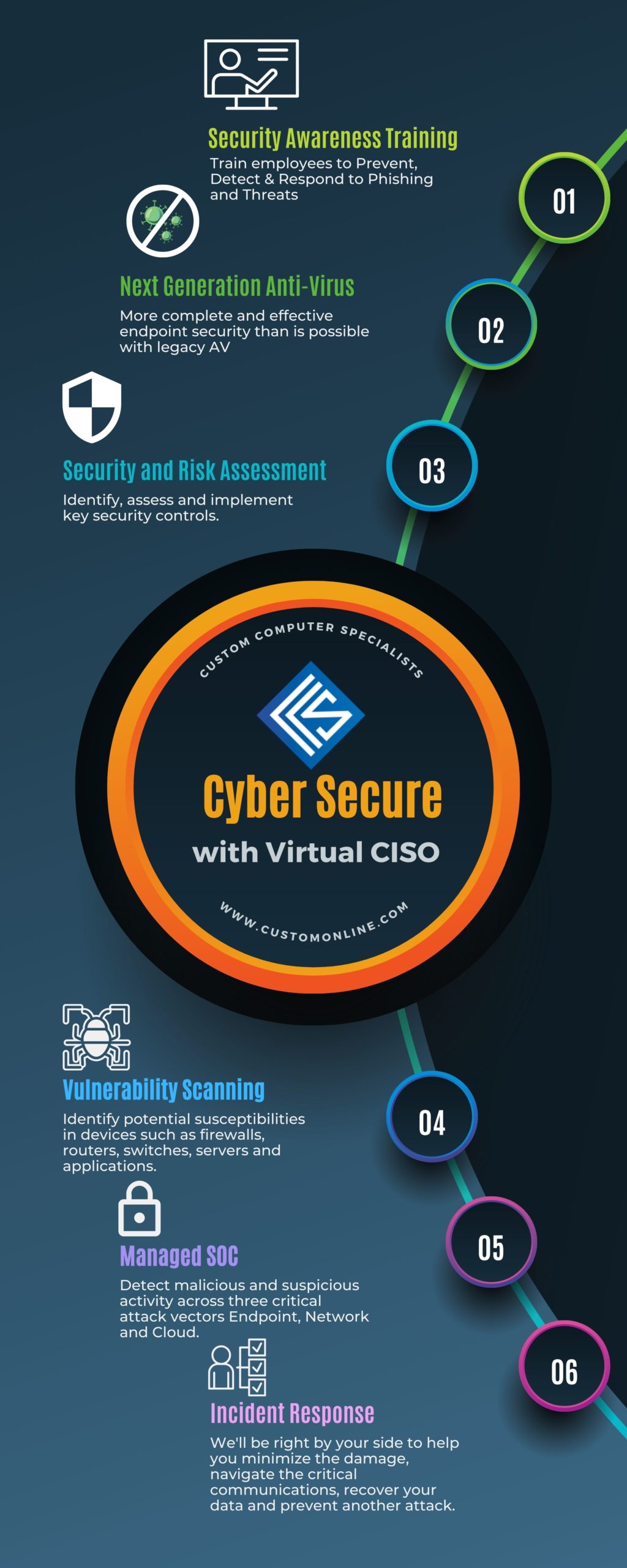
Cyber Secure
There is a delicate balance between locking down your IT infrastructure and maintaining local and remote accessibility. Custom’s Cyber Secure solution is a complete cyber security solution that leverages end-to-end encryption, Virtual Private Networks (VPN) and other best-in-class security practices to help you mitigate your risk of a cyberattack.
We can help you:
-
-
- Train employees to prevent, detect and respond to phishing threats
- Enable secure network access for guests, contractors or partners
- Ensure that software updates are current
- Implement next Generation Anti-Virus for more complete and effective endpoint security
- Identify, assess and implement key security controls
- Identify potential susceptibilities in devices such as firewalls, routers, switches, servers and applications
- Detect malicious and suspicious activity across three critical attack vectors- Enpoint, Network, and Cloud
- Minimize the damage, and navigate the critical commmunications to help you recover your data and prevent another attack
- Assure that your security methods and policies comply with industry and government regulations
- …and more!
-
Physical Security
Whether you’re responsible for securing your data center, personnel access and safety, or surveillance, our security experts can design and install your ideal solution. Perimeter security, video surveillance leveraging Genetec software and Axis or Panasonic video cameras, remotely accessible or closed circuit, electronic door access control, and E-911 over VoIP just scratch the surface.
Our InformaCast Fusion Emergency Notification product alerts those in your school or business of an intruder, emergency situation, severe weather warning, and much more. We can integrate with your existing PA system, telephone network and digital signage while activating a facility-wide lock down and even send notifications to the local police (with video footage of the incident in action). Additional features include active shooter with gun fire detection, IoT integration, scheduled notifications, and a variety of panic button solutions.
Schools, healthcare facilities and businesses place their trust in us to help them mitigate threat risk.
We serve the following regions and states: Long Island, Rhode Island, Massachusetts, New Hampshire, Connecticut, New York, New Jersey
Take our Cyber Readiness Self-Assessment to find out how prepared you are to defend against and recover from a cyber attack.
